SWIFT's 2026 Mandate: How Banks Must Standardize Cyber Incident Response for Enhanced Financial Security

SWIFT incident response standardization represents the most significant cybersecurity mandate facing financial institutions today. The Society for Worldwide Interbank Financial Telecommunication (SWIFT) has established comprehensive requirements through its Customer Security Programme (CSP) framework, demanding that all connected banks implement standardized cyber incident response protocols by 2026.
Financial institutions worldwide face unprecedented cyber threats, with banking networks experiencing a 238% increase in cyberattacks over the past two years. The interconnected nature of global financial systems means that a security breach at any institution can cascade through the entire network, potentially disrupting international money transfers and compromising financial stability.
This mandate addresses critical vulnerabilities in how banks currently manage cybersecurity incidents. Many institutions operate with fragmented response procedures, inconsistent threat intelligence sharing, and varying levels of preparedness that create systemic banking risks across the global financial infrastructure.
The standardization initiative encompasses mandatory incident response planning, regular testing requirements, threat intelligence sharing protocols, and specific documentation standards. Banks must demonstrate compliance through annual SWIFT attestations and independent assessments, with non-compliance potentially resulting in restricted SWIFT network access.
For Chief Information Security Officers (CISOs) and IT directors, understanding and implementing these requirements represents both a compliance necessity and a strategic opportunity to strengthen organizational cybersecurity posture while ensuring continued participation in global financial networks.
The Challenge - Cyber Threats Facing SWIFT Networks
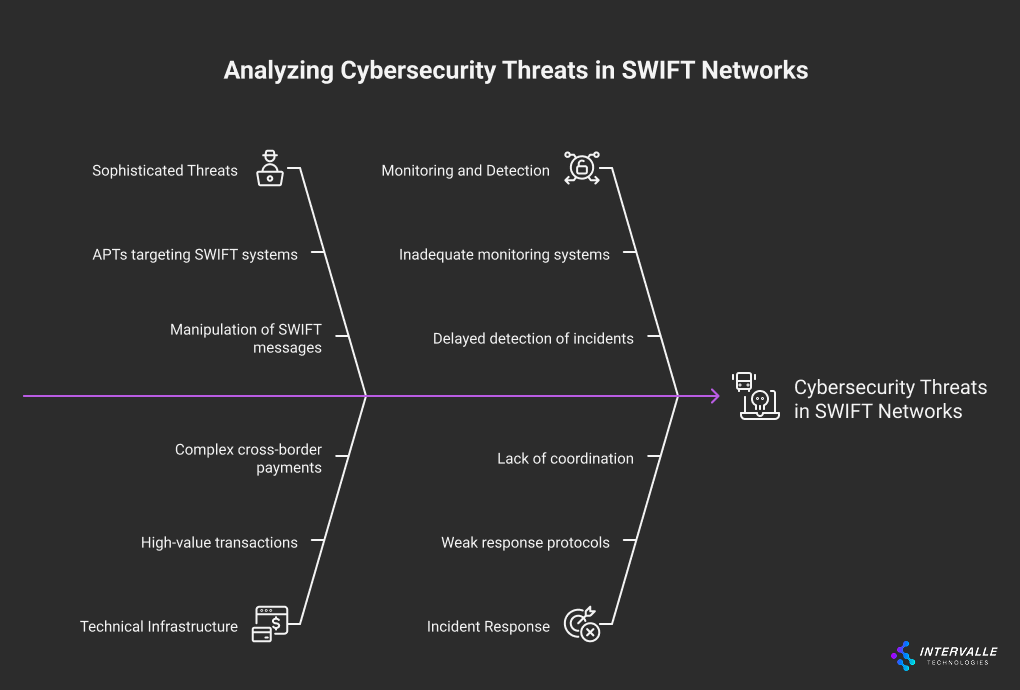
The financial services sector represents the most targeted industry for cybercriminals, accounting for 23% of all cyberattacks globally. Banks connected to the SWIFT network face particularly sophisticated threats that exploit the high-value nature of international financial transactions and the complex technical infrastructure required for cross-border payments.
Recent threat intelligence indicates that Advanced Persistent Threats (APTs) have specifically developed capabilities to target SWIFT messaging systems. The 2016 Bangladesh Bank heist, which resulted in $81 million in stolen funds, demonstrated how attackers could manipulate SWIFT messages to authorize fraudulent transactions. This incident revealed fundamental weaknesses in how financial institutions monitor, detect, and respond to cybersecurity incidents affecting their SWIFT infrastructure.
Advanced Persistent Threats Targeting SWIFT Infrastructure
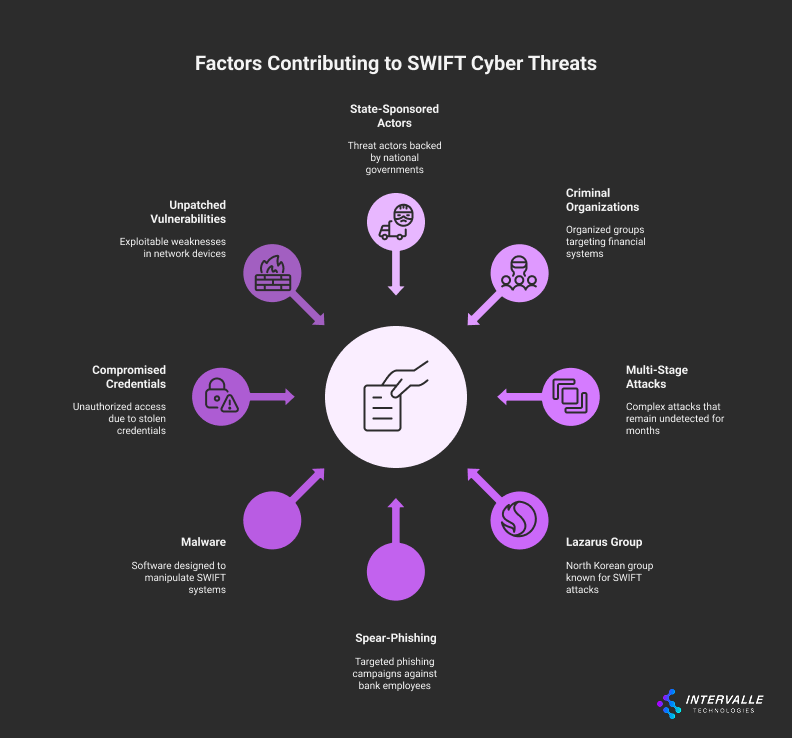
State-sponsored threat actors and sophisticated criminal organizations have developed specialized attack vectors that specifically target SWIFT-connected systems. These threats typically employ multi-stage attack methodologies that can remain undetected for months while attackers conduct reconnaissance and establish persistent access to critical financial systems.
The Lazarus Group, attributed to North Korean state actors, has demonstrated particular expertise in targeting SWIFT infrastructure through techniques including spear-phishing campaigns targeting bank employees with privileged access, malware designed to manipulate SWIFT Alliance Access software, and techniques for bypassing security controls in secure network zones.
Financial institutions report that 67% of successful cyberattacks against their SWIFT infrastructure involved compromised credentials, while 45% exploited unpatched vulnerabilities in network devices protecting the secure zone. These statistics highlight the critical importance of comprehensive incident response planning that can rapidly identify and contain such threats.
Ransomware and Business Email Compromise Incidents
Ransomware attacks against financial institutions have increased by 1,318% since 2020, with attackers specifically targeting backup systems and recovery procedures to maximize damage and increase ransom payment likelihood. Business Email Compromise (BEC) attacks have resulted in $2.4 billion in losses across the financial sector, often serving as initial attack vectors for more sophisticated campaigns targeting SWIFT infrastructure.
The interconnected nature of banking systems means that ransomware incidents can rapidly propagate across multiple institutions through shared infrastructure, correspondent banking relationships, and integrated payment processing systems. Without standardized incident response procedures, banks struggle to coordinate effective containment and recovery efforts during multi-institutional incidents.
Regulatory Pressure and Compliance Gaps
Financial regulators worldwide have intensified cybersecurity oversight following high-profile incidents affecting SWIFT-connected institutions. The European Central Bank's cyber resilience framework, the Federal Reserve's cybersecurity expectations, and similar regulatory initiatives globally require banks to demonstrate mature incident response capabilities.
Current compliance gaps include inconsistent incident classification methodologies, inadequate threat intelligence sharing mechanisms, and insufficient coordination between internal security teams and external stakeholders including law enforcement, regulators, and SWIFT itself. These gaps create regulatory risks that extend beyond cybersecurity concerns to encompass operational risk management and business continuity planning.
Root Causes Behind SWIFT's Standardization Initiative
The decision to mandate standardized incident response procedures stems from systematic vulnerabilities identified across the global financial network. SWIFT's analysis of cybersecurity incidents affecting member institutions revealed fundamental weaknesses in how banks prepare for, detect, respond to, and recover from cyber threats targeting their financial messaging infrastructure.
Technical assessments conducted across multiple regions identified significant variations in cybersecurity maturity levels among SWIFT-connected institutions. Smaller banks and those in emerging markets often lack the resources and expertise necessary to implement sophisticated cybersecurity controls, creating potential entry points for attackers seeking to compromise the broader financial network.
Fragmented Incident Response Approaches Across Institutions
Banking institutions currently employ widely different approaches to cyber incident response, ranging from highly mature Security Operations Centers (SOCs) with 24/7 monitoring capabilities to basic reactive procedures that rely on manual processes and external consultants. This fragmentation creates coordination challenges during multi-institutional incidents and limits the effectiveness of collective defense efforts.
Research indicates that banks with standardized incident response procedures can reduce mean time to detection by 76% and mean time to containment by 84% compared to institutions with ad-hoc response approaches. However, the lack of common frameworks, shared terminology, and interoperable communication protocols has hindered efforts to establish consistent response capabilities across the financial sector.
The absence of standardized incident classification systems means that different institutions may categorize the same type of incident differently, complicating threat intelligence sharing and preventing accurate risk assessment across the network. This inconsistency also affects regulatory reporting, making it difficult for supervisory authorities to maintain comprehensive oversight of cybersecurity risks affecting the financial system.
Information Sharing Limitations in Financial Networks
Effective cybersecurity requires rapid sharing of threat intelligence, including Indicators of Compromise (IOCs), attack techniques, and mitigation strategies. However, legal, regulatory, and competitive concerns have historically limited information sharing between financial institutions, even when facing common threats.
Current threat intelligence sharing initiatives, including SWIFT's own Information Sharing and Analysis Center (ISAC), face adoption challenges due to concerns about liability, confidentiality, and competitive disadvantage. Only 34% of SWIFT-connected institutions actively participate in formal threat intelligence sharing programs, despite evidence that participants experience 58% fewer successful cyberattacks.
The lack of standardized information sharing protocols also means that valuable threat intelligence often arrives too late to be actionable. Manual processes for evaluating, sanitizing, and distributing threat information can take days or weeks, while automated attacks can compromise systems within hours of initial reconnaissance.
Skills Gaps in Cybersecurity Workforce
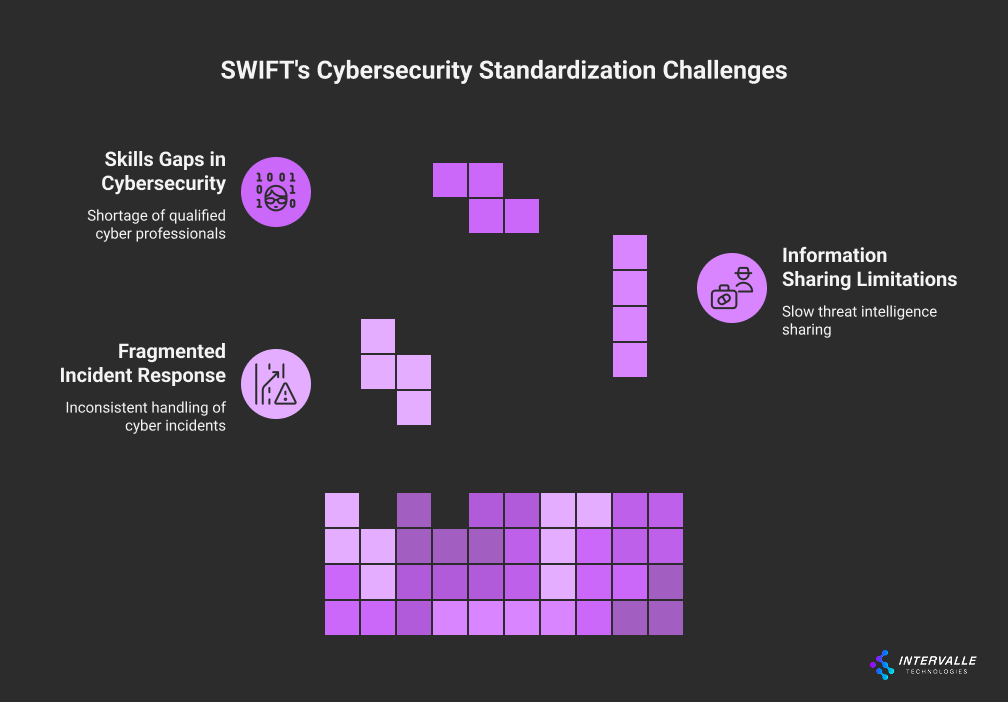
The global shortage of qualified cybersecurity professionals particularly affects financial institutions, which require specialized expertise in both cybersecurity and financial systems. The complexity of SWIFT infrastructure demands professionals who understand both network security principles and the specific requirements of international financial messaging.
Current workforce analysis indicates that 68% of banks report difficulty recruiting qualified cybersecurity professionals, while 43% cite skills gaps in incident response as their most significant cybersecurity challenge. The specialized nature of SWIFT security requirements means that many cybersecurity professionals require additional cybersecurity training to effectively protect financial messaging infrastructure.
The standardization of incident response procedures will help address these workforce challenges by establishing clear role definitions, standardized training requirements, and common competency frameworks that enable more efficient resource allocation and professional development across the financial sector.
Actionable Solutions and Implementation Frameworks
SWIFT's Customer Security Programme provides a comprehensive framework for implementing standardized cyber incident response capabilities across financial institutions. The mandatory controls establish minimum requirements while allowing institutions to enhance their capabilities based on specific risk profiles and operational requirements.
The framework emphasizes a risk-based approach that enables institutions to prioritize implementation efforts based on their specific threat landscape, technical architecture, and business requirements. This flexibility ensures that both large international banks and smaller regional institutions can achieve compliance while optimizing resource allocation and operational efficiency.
Mandatory Incident Response Planning Components
Control 7.1 of the SWIFT Customer Security Programme mandates that all institutions develop and maintain comprehensive cyber incident response plans that address the specific requirements of SWIFT-connected infrastructure. These plans must include detailed procedures for incident detection, containment, investigation, recovery, and post-incident analysis.
The incident response plan must include up-to-date contact information for internal and external stakeholders, including SWIFT Customer Support Centre, regulatory authorities, law enforcement agencies, and third-party service providers. Escalation procedures must specify clear timelines and decision-making authority to ensure rapid response during critical incidents.
Notification requirements mandate prompt communication with multiple stakeholders simultaneously. Banks must notify internal leadership, regulatory authorities, law enforcement, and SWIFT Customer Support through designated channels within specified timeframes. The plan must also include procedures for coordinating with forensic investigators and maintaining evidence preservation standards required for legal proceedings.
Containment procedures must balance the need for rapid isolation of compromised systems with the requirement to maintain business continuity and preserve forensic evidence. The framework requires institutions to develop specific procedures for different incident types, including malware infections, unauthorized access, data exfiltration, and system availability disruptions.
Testing and Documentation Standards
The framework mandates regular testing of incident response procedures through tabletop exercises, technical simulations, and full-scale response drills. Testing must occur at least every two years, with comprehensive reviews following each exercise to identify improvement opportunities and update procedures based on lessons learned.
Documentation requirements extend beyond basic procedural manuals to include detailed incident logs, decision-making rationale, communication records, and post-incident analysis reports. This documentation serves multiple purposes including regulatory compliance, insurance claims, legal proceedings, and continuous improvement efforts.
The testing program must evaluate both technical response capabilities and organizational coordination procedures. Technical testing should include scenarios involving different attack vectors, system compromise levels, and recovery requirements. Organizational testing must validate communication procedures, decision-making processes, and coordination with external stakeholders.
Threat Intelligence Integration Protocols
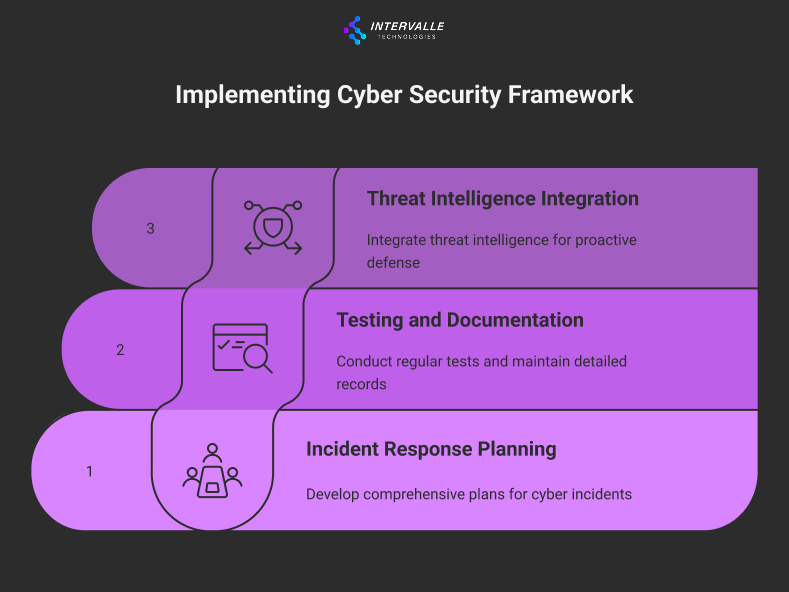
The framework requires institutions to establish formal procedures for consuming and contributing to threat intelligence sharing initiatives. Banks must implement technical capabilities to receive automated threat intelligence feeds and integrate IOCs into their security monitoring systems.
Institutions must develop procedures for evaluating threat intelligence relevance, implementing protective measures, and sharing anonymized incident information with the broader financial community. The framework emphasizes the importance of timely information sharing while respecting legal, regulatory, and confidentiality requirements.
Technical implementation must include automated systems for blocking malicious IP addresses and URLs identified in threat intelligence feeds. The framework also requires procedures for manual analysis of complex threats that require human expertise to evaluate and respond to effectively.
Advanced institutions should consider implementing Security Orchestration, Automation, and Response (SOAR) platforms that can automatically consume threat intelligence feeds, correlate information with internal security events, and initiate predetermined response actions. These capabilities significantly reduce response times and ensure consistent application of threat intelligence across the organization.
Real-World Implementation Strategies
Successful implementation of SWIFT's incident response requirements demands a structured approach that addresses both technical and organizational challenges. Banks must develop comprehensive project plans that account for resource constraints, regulatory timelines, and operational continuity requirements while building sustainable cybersecurity capabilities.
The most effective implementation strategies employ phased approaches that begin with foundational capabilities and gradually build more sophisticated response and recovery procedures. This methodology allows institutions to achieve compliance milestones while developing internal expertise and testing procedures under controlled conditions.
Phased Implementation Timeline for Banks

Phase one focuses on establishing core incident response capabilities including policy development, team formation, and basic training programs. Institutions should begin by conducting gap assessments against SWIFT requirements and developing detailed implementation roadmaps with specific milestones and resource requirements.
During the initial phase, banks should establish incident response teams with clearly defined roles and responsibilities. Team composition should include representatives from information security, IT operations, legal, compliance, communications, and executive management. External relationships with forensic investigators, legal counsel, and regulatory contacts should also be established during this phase.
Phase two involves implementing technical capabilities including security monitoring systems, threat intelligence integration, and automated response procedures. Banks should prioritize detection capabilities that can identify threats specific to SWIFT infrastructure while ensuring integration with existing security operations workflows.
Technical implementation should include deployment of specialized monitoring tools for SWIFT messaging systems, network segmentation verification, and endpoint detection capabilities for systems with access to the secure zone. Integration with SIEM platforms enables correlation of security events across multiple systems and supports automated alerting procedures.
Phase three focuses on testing, refinement, and continuous improvement of incident response capabilities. Regular testing exercises should begin with simple tabletop discussions and progress to complex technical simulations that test both individual and organizational response capabilities.
Intervalle Technologies has observed that banks achieving the most effective implementations dedicate approximately 18-24 months to complete all three phases, with ongoing maintenance and improvement efforts continuing beyond initial compliance achievement. Organizations that attempt accelerated implementation often experience gaps in training, testing, or documentation that create compliance risks and operational challenges.
For institutions requiring specialized expertise in SWIFT CSP audits, comprehensive assessment services ensure alignment with all mandatory controls while identifying optimization opportunities that enhance both compliance and operational effectiveness.
Future Outlook and Strategic Recommendations
The standardization of incident response procedures represents the beginning of a broader transformation in how financial institutions approach cybersecurity risk management. Industry trends indicate increasing integration of artificial intelligence and machine learning capabilities in threat detection and response, automated threat intelligence sharing, and collaborative defense initiatives across the financial sector.
Regulatory expectations will continue evolving beyond basic compliance requirements toward outcome-based assessments that evaluate the actual effectiveness of cybersecurity programs. Banks should anticipate requirements for demonstrating measurable improvements in detection capabilities, response times, and recovery procedures through quantitative metrics and comparative benchmarking.
The emergence of quantum computing capabilities will require significant updates to cryptographic systems used in financial messaging, necessitating coordinated transition planning across the global financial network. Incident response procedures must evolve to address quantum-resistant cryptography implementation challenges and potential vulnerabilities during transition periods.
Strategic recommendations for banking leadership include investment in automation capabilities that can reduce manual effort required for routine incident response tasks, development of internal cybersecurity expertise through targeted hiring and cybersecurity training programs, and establishment of strategic partnerships with specialized service providers including Intervalle Technologies for complex technical assessments and implementation support.
Banks should also consider the broader business benefits of enhanced cybersecurity capabilities including improved operational resilience, reduced insurance premiums, enhanced customer confidence, and competitive advantages in serving security-conscious clients. Implementing comprehensive cybersecurity frameworks often justifies investments beyond minimum compliance requirements through measurable ROI improvements.
Conclusion
SWIFT's 2026 incident response mandate represents a critical inflection point for global banking cybersecurity, requiring institutions to move beyond fragmented approaches toward standardized, tested, and documented response capabilities. The framework addresses systemic vulnerabilities that have enabled sophisticated attacks against financial infrastructure while providing flexibility for institutions to enhance capabilities based on specific risk profiles.
Successful implementation requires comprehensive planning, adequate resource allocation, and sustained commitment from executive leadership. Banks that begin implementation planning immediately will have sufficient time to develop mature capabilities, conduct thorough testing, and achieve compliance without operational disruption.
The standardization initiative creates opportunities for enhanced collaboration, improved threat intelligence sharing, and strengthened collective defense across the financial sector. Institutions that embrace these requirements as strategic investments rather than compliance obligations will achieve superior cybersecurity outcomes and operational resilience.
Financial institutions seeking expert guidance on SWIFT incident response implementation should engage specialized cybersecurity consultants with proven experience in financial services regulatory compliance and technical implementation. The complexity of these requirements demands expertise that combines deep understanding of SWIFT infrastructure with practical experience in incident response program development.
Contact Intervalle Technologies today to discuss your SWIFT incident response implementation strategy and ensure your institution meets the 2026 compliance deadline while building world-class cybersecurity capabilities that protect your organization and strengthen the global financial network.
